CryptoDB
Witness Indistinguishability for Any Single-Round Argument with Applications to Access Control
| Authors: | |
|---|---|
| Download: | |
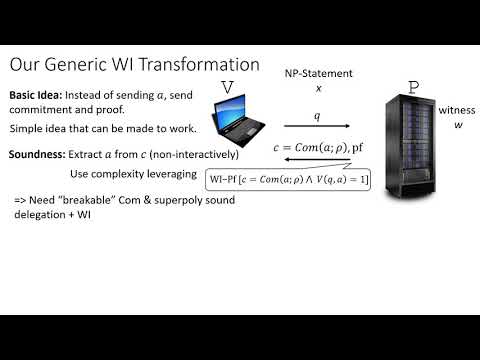
| Abstract: | Consider an access policy for some resource which only allows access to users of the system who own a certain set of attributes. Specifically, we consider the case where such an access structure is defined by some monotone function $$f:{0,1}^N ightarrow {0,1}$$ , belonging to some class of function $$F$$ (e.g. conjunctions, space bounded computation), where N is the number of possible attributes. In this work we show that any succinct single-round delegation scheme for the function class $$F$$ can be converted into a succinct single-round private access control protocol. That is, a verifier can be convinced that an approved user (i.e. one which holds an approved set of attributes) is accessing the system, without learning any additional information about the user or the set of attributes. As a main tool of independent interest, we show that assuming a quasi-polynomially secure two-message oblivious transfer scheme with statistical sender privacy (which can be based on quasi-polynomial hardness of the DDH, QR, DCR or LWE assumptions), we can convert any single-round protocol into a witness indistinguishable one, with similar communication complexity. |
Video from PKC 2020
BibTeX
@article{pkc-2020-30306,
title={Witness Indistinguishability for Any Single-Round Argument with Applications to Access Control},
booktitle={Public-Key Cryptography – PKC 2020},
series={Public-Key Cryptography – PKC 2020},
publisher={Springer},
volume={12111},
pages={97-123},
doi={10.1007/978-3-030-45388-6_4},
author={Zvika Brakerski and Yael Tauman Kalai},
year=2020
}