CryptoDB
Side-Channel Protections for Picnic Signatures
| Authors: |
|
|---|---|
| Download: | |
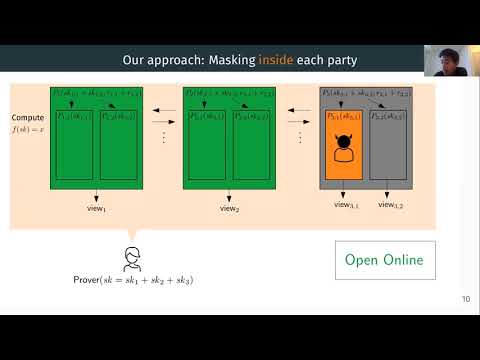
| Abstract: | We study masking countermeasures for side-channel attacks against signature schemes constructed from the MPC-in-the-head paradigm, specifically when the MPC protocol uses preprocessing. This class of signature schemes includes Picnic, an alternate candidate in the third round of the NIST post-quantum standardization project. The only previously known approach to masking MPC-in-the-head signatures suffers from interoperability issues and increased signature sizes. Further, we present a new attack to demonstrate that known countermeasures are not sufficient when the MPC protocol uses a preprocessing phase, as in Picnic3.We overcome these challenges by showing how to mask the underlying zero-knowledge proof system due to Katz–Kolesnikov–Wang (CCS 2018) for any masking order, and by formally proving that our approach meets the standard security notions of non-interference for masking countermeasures. As a case study, we apply our masking technique to Picnic. We then implement different masked versions of Picnic signing providing first order protection for the ARM Cortex M4 platform, and quantify the overhead of these different masking approaches. We carefully analyze the side-channel risk of hashing operations, and give optimizations that reduce the CPU cost of protecting hashing in Picnic by a factor of five. The performance penalties of the masking countermeasures ranged from 1.8 to 5.5, depending on the degree of masking applied to hash function invocations. |
Video from TCHES 2021
BibTeX
@article{tches-2021-31317,
title={Side-Channel Protections for Picnic Signatures},
journal={IACR Transactions on Cryptographic Hardware and Embedded Systems},
publisher={Ruhr-Universität Bochum},
volume={2021, Issue 4},
pages={239-282},
url={https://tches.iacr.org/index.php/TCHES/article/view/9066},
doi={10.46586/tches.v2021.i4.239-282},
author={Diego F. Aranha and Sebastian Berndt and Thomas Eisenbarth and Okan Seker and Akira Takahashi and Luca Wilke and Greg Zaverucha},
year=2021
}