CryptoDB
Weak Tweak-Keys for the CRAFT Block Cipher
| Authors: |
|
|---|---|
| Download: | |
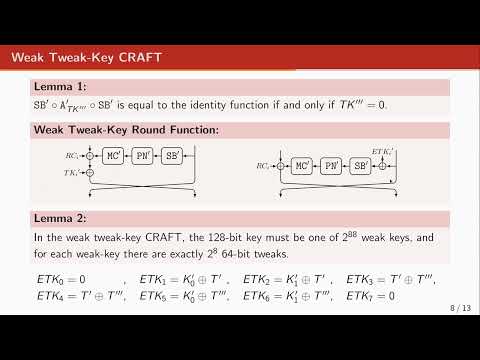
| Abstract: | CRAFT is a lightweight tweakable Substitution-Permutation-Network (SPN) block cipher optimized for efficient protection of its implementations against Differential Fault Analysis (DFA) attacks. In this paper, we present an equivalent description of CRAFT up to a simple mapping on the plaintext, ciphertext and round tweakeys. We show that the new representation, for a sub-class of keys, leads to a new structure which is a Feistel network, with non-linear operation and key addition only on half the state. Consequently, it reveals a class of weak keys for which CRAFT is less resistant against differential and linear cryptanalyses. As a result, we present one weak-key single-tweak differential attack on 23 rounds (with time complexity of 294 encryptions and data complexity of 274 chosen plaintext/tweak/ciphertext tuples and works for 2112 weak keys) and one weak-key related-tweak attack on 26 rounds of the cipher (with time complexity of 2105 encryptions and data complexity 273 chosen plaintext/tweak/ciphertext tuples and works for 2108 weak keys). Note that these attacks do not break the security claim of the CRAFT block cipher. |
Video from TOSC 2022
BibTeX
@article{tosc-2022-31972,
title={Weak Tweak-Keys for the CRAFT Block Cipher},
journal={IACR Transactions on Symmetric Cryptology},
publisher={Ruhr-Universität Bochum},
volume={2022, Issue 1},
pages={38-63},
url={https://tosc.iacr.org/index.php/ToSC/article/view/9526},
doi={10.46586/tosc.v2022.i1.38-63},
author={Gregor Leander and Shahram Rasoolzadeh},
year=2022
}