CryptoDB
Low Communication Complexity Protocols, Collision Resistant Hash Functions and Secret Key-Agreement Protocols
| Authors: |
|
|---|---|
| Download: | |
| Conference: | CRYPTO 2022 |
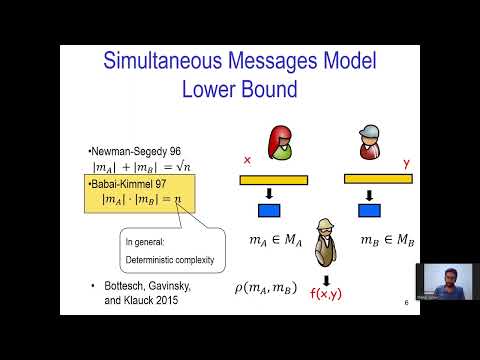
| Abstract: | We study communication complexity in computational settings where bad inputs may exist, but they should be hard to find for any computationally bounded adversary. We define a model where there is a source of public randomness but the inputs are chosen by a computationally bounded adversarial participant \emph{after seeing the public randomness}. We show that breaking some known communication lower bounds in this model is closely connected to known cryptographic assumptions. We consider the simultaneous messages model and the interactive communication model and show that for any non trivial predicate (such as equality): 1. Breaking the \Omega(\sqrt n) bound in the simultaneous message case or the \Omega(\log n) bound in the interactive communication case, implies the existence of distributional collision-resistant hash functions (dCRH). Note that with a CRH the lower bounds can be broken. This is shown using techniques from Babai and Kimmel [CCC 1997]. 2. There are no protocols of constant communication in this preset randomness settings (unlike the plain public randomness model). The other model we study is that of a stateful ``free talk", where participants can communicate freely \emph{before} the inputs are chosen and may maintain a state, and the communication complexity is measured only afterwards. We show that efficient protocols for equality in this model imply secret key-agreement protocols (in a constructive sense). On the other hand, secret key-agreement protocols imply optimal in terms of error protocols for equality. |
Video from CRYPTO 2022
BibTeX
@inproceedings{crypto-2022-32206,
title={Low Communication Complexity Protocols, Collision Resistant Hash Functions and Secret Key-Agreement Protocols},
publisher={Springer-Verlag},
author={Shahar Cohen and Moni Naor},
year=2022
}