CryptoDB
New Slide Attacks on Almost Self-Similar Ciphers
| Authors: |
- Orr Dunkelman , University of Haifa
- Nathan Keller , Bar-Ilan University
- Noam Lasry , Bar-Ilan University
- Adi Shamir , Weizmann Institute of Science
|
| Download: |
- DOI: 10.1007/978-3-030-45721-1_10
(login may be required)
- Search ePrint
- Search Google
|
| Presentation: |
Slides
|
|
Conference:
|
EUROCRYPT 2020
|
| Abstract: |
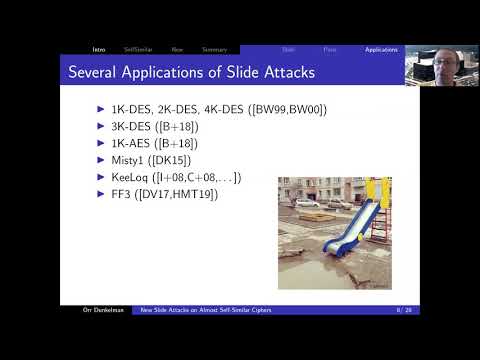
The slide attack is a powerful cryptanalytic tool which has the unusual property that it can break iterated block ciphers with a complexity that does not depend on their number of rounds. However, it requires complete self similarity in the sense that all the rounds must be identical. While this can be the case in Feistel structures, this rarely happens in SP networks since the last round must end with an additional post-whitening subkey. In addition, in many SP networks the final round has additional asymmetries - for example, in AES the last round omits the MixColumns operation. Such asymmetry in the last round can make it difficult to utilize most of the advanced tools which were developed for slide attacks, such as deriving from one slid pair additional slid pairs by repeatedly
re-encrypting their ciphertexts. Consequently, almost all the successful applications of slide attacks against real cryptosystems (e.g., FF3, GOST,
SHACAL-1, etc.) had targeted Feistel structures rather than SP networks.
In this paper we overcome this last round problem by developing four new types of slide attacks. We demonstrate their power by applying them to many types of AES-like structures (with and without linear mixing in the last round, with known or secret S-boxes, with periodicity of 1,2 and 3 in their subkeys, etc).
In most of these cases, the time complexity of our attack is close to $2^{n/2}$, the smallest possible complexity for most slide attacks. Our new slide attacks have several unique properties: The first uses slid sets in which each plaintext from the first set forms a slid pair with some plaintext from the second set, but without knowing the exact correspondence. The second makes it possible to create from several slid pairs an exponential number of new slid pairs which form a hypercube spanned by the given pairs. The third has the unusual property that it is always successful, and the fourth can use known messages instead of chosen messages, with only slightly higher time complexity. |
Video from EUROCRYPT 2020
BibTeX
@inproceedings{eurocrypt-2020-30233,
title={New Slide Attacks on Almost Self-Similar Ciphers},
booktitle={39th Annual International Conference on the Theory and Applications of Cryptographic Techniques, Zagreb, Croatia, May 10–14, 2020, Proceedings},
series={Lecture Notes in Computer Science},
publisher={Springer},
keywords={Cryptanalysis;Slide Attacks;SPNs;1K-AES;2K-AES;3K-AES},
volume={12105},
doi={10.1007/978-3-030-45721-1_10},
author={Orr Dunkelman and Nathan Keller and Noam Lasry and Adi Shamir},
year=2020
}